My inbox has been flooded with emails of support, encouragement and best wishes from friends, family and people from around the world. The paypal legal defense fund is doing pretty well - and thus I thank everyone who has donated to the fund.
While the university's legal team have said they won't protect me - the professors/students here at IU have been amazingly supportive, esp. those in my department and my adviser in particular.
Members of the press: I really can't comment right now. Even if you send me an email saying you're on my side, I still can't comment. I urge you to read this blog going back for the last week or so, and top-notch coverage by places like Wired News and BoingBoing.
However, I can at least tell you that my last name is pronounced Soh-Goy-An.
Monday, October 30, 2006
Sunday, October 29, 2006
A bit of good news
Markey announced his change of heart Sunday morning in a press release:
On Friday I urged the Bush Administration to ‘apprehend’ and shut down whoever had created a new website that enabled persons without a plane ticket to easily fake a boarding pass and use it to clear security, gain access to the boarding area and potentially to the cabin of a passenger plane. Subsequently I learned that the person responsible was a student at Indiana University, Christopher Soghoian, who intended no harm but, rather, intended to provide a public service by warning that this long-standing loophole could be easily exploited. The website has now apparently been shut down.
Under the circumstances, any legal consequences for this student must take into account his intent to perform a public service, to publicize a problem as a way of getting it fixed. He picked a lousy way of doing it, but he should not go to jail for his bad judgment. Better yet, the Department of Homeland Security should put him to work showing public officials how easily our security can be compromised.
It remains a fact that fake boarding passes can be easily created and the integration of terrorist watch lists with boarding security is still woefully inadequate. The best outcome of Mr. Soghoian’s ill-considered demonstration would be for the Department of Homeland Security to close these loopholes immediately.
More here
On Friday I urged the Bush Administration to ‘apprehend’ and shut down whoever had created a new website that enabled persons without a plane ticket to easily fake a boarding pass and use it to clear security, gain access to the boarding area and potentially to the cabin of a passenger plane. Subsequently I learned that the person responsible was a student at Indiana University, Christopher Soghoian, who intended no harm but, rather, intended to provide a public service by warning that this long-standing loophole could be easily exploited. The website has now apparently been shut down.
Under the circumstances, any legal consequences for this student must take into account his intent to perform a public service, to publicize a problem as a way of getting it fixed. He picked a lousy way of doing it, but he should not go to jail for his bad judgment. Better yet, the Department of Homeland Security should put him to work showing public officials how easily our security can be compromised.
It remains a fact that fake boarding passes can be easily created and the integration of terrorist watch lists with boarding security is still woefully inadequate. The best outcome of Mr. Soghoian’s ill-considered demonstration would be for the Department of Homeland Security to close these loopholes immediately.
More here
A couple things
For those of you who do not want/cannot interact with Paypal, donations to the legal defense fund can also be sent to:
Christopher Soghoian
School of Informatics
Indiana University
901 E 10th St
Bloomington, Indiana 47408
USA
Please put my name as payable to.
The legal advice I've gotten thus far has been to not talk to the press for now.
Christopher Soghoian
School of Informatics
Indiana University
901 E 10th St
Bloomington, Indiana 47408
USA
Please put my name as payable to.
The legal advice I've gotten thus far has been to not talk to the press for now.
Saturday, October 28, 2006
FBI Visit #2
I didn't sleep at home last night. It's fair to say I was rather shaken up.
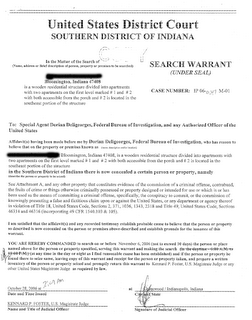
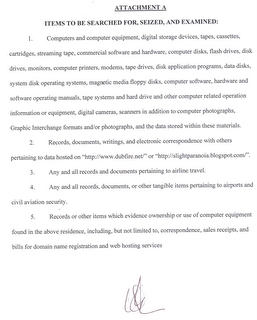
I came back today, to find the glass on the front door smashed.
Inside, is a rather ransacked home, a search warrant taped to my kitchen table, a total absence of computers - and various other important things. I have no idea what time they actually performed the search, but the warrant was approved at 2AM. I'm sincerely glad I wasn't in bed when they raided the house. That would have been even more scary.
I'm trying to maintain a semi-normal life. I have grad-student work to do - and a conference deadline of Nov 20th for a paper I'm working on.
Legal Defense Fund
I'm still waiting for callbacks from potential pro-bono lawyers.
However, this could very well turn out to be an extremely expensive experience. I'm a grad student, and the university has been very straight forward about the fact that they won't cover my legal bills, or protect me themselves.
Thus, I've thrown together a Legal Defense Fund via Paypal. Any money donated will go towards my legal costs - and if for some reason, I come out of this unscathed and with remaining funds in the account - It'll donate it all to the EFF, or some other pro privacy/freedom group.
(Broken paypal link fixed. Thanks for the feedback!)
Also: There's now a "Keep Chris out of Jail" facebook group.
However, this could very well turn out to be an extremely expensive experience. I'm a grad student, and the university has been very straight forward about the fact that they won't cover my legal bills, or protect me themselves.
Thus, I've thrown together a Legal Defense Fund via Paypal. Any money donated will go towards my legal costs - and if for some reason, I come out of this unscathed and with remaining funds in the account - It'll donate it all to the EFF, or some other pro privacy/freedom group.
(Broken paypal link fixed. Thanks for the feedback!)
Also: There's now a "Keep Chris out of Jail" facebook group.
Friday, October 27, 2006
Post FBI Visit
The FBI visited.
They handed me with a written order to remove the boarding pass generator. By the time we were somewhere with internet access, the website had already been taken down.
I am now safe (and no longer with the FBI).
Still trying to find a lawyer.....
Edit:
If you want to help, a good start would be to email Congressman Markey - who initially called for my arrest.
They handed me with a written order to remove the boarding pass generator. By the time we were somewhere with internet access, the website had already been taken down.
I am now safe (and no longer with the FBI).
Still trying to find a lawyer.....
Edit:
If you want to help, a good start would be to email Congressman Markey - who initially called for my arrest.
Congressman calls for my arrest
As reported by Wired News and ABC News:
"The Bush Administration must immediately act to investigate, apprehend those responsible, shut down the website, and warn airlines and aviation security officials to be on the look-out for fraudsters or terrorists trying to use fake boarding passes in an attempt to cheat their way through security and onto a plane," Markey said in a statement. "There are enough loopholes at the backdoor of our passenger airplanes from not scanning cargo for bombs; we should not tolerate any new loopholes making it easier for terrorists to get into the front door of a plane."
In addition to calling for my arrest, the congressman may want to call for the arrest of Senator Schumer (D-NY). In April of this year, he posted rather detailed instructions for the exact same attack. See: here. Sure, he didn't produce a php script that'd do it for you, but he provided detailed enough instructions that a terrorist or evil-doer with basic computer skills could do it.
Perhaps he'll be my cell-mate.
In all seriousness, Indiana University's legal team have essentially said I'm on my own. Thus, if this issue becomes serious, and the feds knock at my door, any offers of pro-bono legal assistance would be much appreciated.
Also - just for the record: I have not flown, or even attempted to enter the airport with one of these fake boarding passes. I haven't even printed one out. All I have done is create a php script, which highlights a security hole made public by others before me.
"The Bush Administration must immediately act to investigate, apprehend those responsible, shut down the website, and warn airlines and aviation security officials to be on the look-out for fraudsters or terrorists trying to use fake boarding passes in an attempt to cheat their way through security and onto a plane," Markey said in a statement. "There are enough loopholes at the backdoor of our passenger airplanes from not scanning cargo for bombs; we should not tolerate any new loopholes making it easier for terrorists to get into the front door of a plane."
In addition to calling for my arrest, the congressman may want to call for the arrest of Senator Schumer (D-NY). In April of this year, he posted rather detailed instructions for the exact same attack. See: here. Sure, he didn't produce a php script that'd do it for you, but he provided detailed enough instructions that a terrorist or evil-doer with basic computer skills could do it.
Perhaps he'll be my cell-mate.
In all seriousness, Indiana University's legal team have essentially said I'm on my own. Thus, if this issue becomes serious, and the feds knock at my door, any offers of pro-bono legal assistance would be much appreciated.
Also - just for the record: I have not flown, or even attempted to enter the airport with one of these fake boarding passes. I haven't even printed one out. All I have done is create a php script, which highlights a security hole made public by others before me.
Wednesday, October 25, 2006
Airport (in)security for the masses
I realized today that editing HTML, while easy enough for a geek, is still far too difficult for population at large.
And thus, I now present: Chris's Northwest Airlines Boarding Pass Generator
Using this, you can:
1. Meet your elderly grandparents at the gate
2. 'Upgrade' yourself once on the airplane - by printing another boarding pass for a ticket you're already purchased, only this time, in Business Class.
3. Demonstrate that the TSA Boarding Pass/ID check is useless.
Have fun!
And thus, I now present: Chris's Northwest Airlines Boarding Pass Generator
Using this, you can:
1. Meet your elderly grandparents at the gate
2. 'Upgrade' yourself once on the airplane - by printing another boarding pass for a ticket you're already purchased, only this time, in Business Class.
3. Demonstrate that the TSA Boarding Pass/ID check is useless.
Have fun!
Monday, October 23, 2006
A few useful applescripts
I sat next to Paul Syverson at the WESII workshop in Washington DC today.
During a discussion of Firefox/Safari, he remarked that it'd be really neat if something like Tor Button existed for the Safari Web browser (which instead of using its own proxy settings relies upon the OS's settings).
A an hour later, and after a bit if hackery, I present the following:
A script that toggles the proxy settings in Mac OSX (Tiger) on/off for Tor:
As a script and As an application that you can double-click on.
There's also a very useful script available elsewhere which will start Safari in private browsing mode by default.
One item of frustration is that to get any of the scripts to work, you must set the "Enable access for assistive devices" feature in the "Universal Access" system preference. Without this, nothing will work.
This appears to be a reasonably valid security preference in the OS. Without this option, scripts cannot control various elements of the user-interface.
During a discussion of Firefox/Safari, he remarked that it'd be really neat if something like Tor Button existed for the Safari Web browser (which instead of using its own proxy settings relies upon the OS's settings).
A an hour later, and after a bit if hackery, I present the following:
A script that toggles the proxy settings in Mac OSX (Tiger) on/off for Tor:
As a script and As an application that you can double-click on.
There's also a very useful script available elsewhere which will start Safari in private browsing mode by default.
One item of frustration is that to get any of the scripts to work, you must set the "Enable access for assistive devices" feature in the "Universal Access" system preference. Without this, nothing will work.
This appears to be a reasonably valid security preference in the OS. Without this option, scripts cannot control various elements of the user-interface.
Friday, October 20, 2006
Bumped 3x in 2 days
When I flew out of Indianapolis a month ago, I was told that there was no way for me to opt out of the air puffer machine used at the airport - as I was a SSSS (secondary screening selectee) due to not showing any ID.
Well, the security line at Indianapolis on Thursday was freakishly long, and although I had already made my mind up to be a good boy and follow the rules earlier in the morning, I changed my mind when I saw the line.
The airline gave me a special no-id boarding pass, and thus I was able to bypass the entire security line, and go straight through the special selectee line. W00t!
Much to my pleasant surprise, this time, no one batted an eyelid when I declined to go through the air puffer machine. I'm not sure if they have changed their policies, have new staff who do not know the rules, or I was lied to before. But I'll be calling TSA up when I get back to Indiana next week.
In other news - my flight to DC was oversold, and so I gave up my seat - and flew into DC 3 hours later. In exchange for suffering this delay, I was given a free round-trip ticket anywhere in the US on Northwest.
Today, sitting at Baltimore airport with my girlfriend, we gave up our seats once, and are waiting for the next flight - which is also looking oversold. If it works out, we'll get 2 free round-trip tickets each (we have one each already from the first flight today).
Which will mean 3 free round trip tickets earned in 2 days of airport shenanigans.
For those stuck in airports:
Northwest has free wireless access in their lounges. Sit outside and you can mouch signal.
United/US airways has t-mobile wifi in their lounges, and you can sign up for a free 30 day trial using this link: https://selfcare.hotspot.t-mobile.com/accountcreate/ExternalSetPromotionCode.do?promo=KD1MTH105
It makes the time just fly by.
Well, the security line at Indianapolis on Thursday was freakishly long, and although I had already made my mind up to be a good boy and follow the rules earlier in the morning, I changed my mind when I saw the line.
The airline gave me a special no-id boarding pass, and thus I was able to bypass the entire security line, and go straight through the special selectee line. W00t!
Much to my pleasant surprise, this time, no one batted an eyelid when I declined to go through the air puffer machine. I'm not sure if they have changed their policies, have new staff who do not know the rules, or I was lied to before. But I'll be calling TSA up when I get back to Indiana next week.
In other news - my flight to DC was oversold, and so I gave up my seat - and flew into DC 3 hours later. In exchange for suffering this delay, I was given a free round-trip ticket anywhere in the US on Northwest.
Today, sitting at Baltimore airport with my girlfriend, we gave up our seats once, and are waiting for the next flight - which is also looking oversold. If it works out, we'll get 2 free round-trip tickets each (we have one each already from the first flight today).
Which will mean 3 free round trip tickets earned in 2 days of airport shenanigans.
For those stuck in airports:
Northwest has free wireless access in their lounges. Sit outside and you can mouch signal.
United/US airways has t-mobile wifi in their lounges, and you can sign up for a free 30 day trial using this link: https://selfcare.hotspot.t-mobile.com/accountcreate/ExternalSetPromotionCode.do?promo=KD1MTH105
It makes the time just fly by.
Wednesday, October 18, 2006
Paging Osama, please meet your party at the Information Desk
[Ed: The technique outlined in this blog post was also documented by a journalist at Slate last year. See: http://www.slate.com/id/2113157/
The only way for these kind of problems to get fixed, are through through public full disclosure. TSA/DHS cannot be expected to fix anything unless they are publicly shamed into doing so.]
Shortly after 9/11, the airlines introduced a very reasonable security check (amongst a bunch of other stupid ones): They started checking ID at the gate.
It's really important to note why this is good. You see, when they scan your boarding pass, the screen will either beep yes, to tell them it's valid, or beep no, and tell them that it's a bogus pass. They'll be able to look on their terminal, see the name attached to the booking reference, and check it against the ID in front of them (ok, they rarely did this, and instead checked the name on the boarding pass - but at least they had the potential to do it correctly).
However, checking the ID of 300 passengers when you're trying to fill up and airplane can lead to considerable delays, and thus, once the hysteria of a few terrorists armed with exacto blades had calmed down, the airlines did away with this requirement, and instead offloaded it to TSA.
Herein lies the problem: TSA doesn't have access to the Airline's computer systems. Thus, they have no real way of knowing if a boarding pass is real or not. All they can do is verify that the name on the piece of paper (which may or may not be a boarding pass) matches the ID they have been given.
This situtation is made even worse when you consider the fact that you can print your own boarding pass online at home. This is often a bunch of text/html, with one or two images (a barcode, and perhaps an airline logo). It is trivially easy - as in, 20 seconds with a text-editor, and not even requiring you to open photoshop - to open it up, and change the name.
And thus, I introduce a perfectly valid method for a terrorist - known to the government, and already on the domestic no fly list, to board a US commercial flight.
Step 1. Purchase an airplane ticket in the name of "George P. Watkins"
Step 2. Check-in online the night before, and print out your boarding pass online.
Step 3. Save as HTML, edit the boarding pass code, and change it to your real name "Ali Terrorist"
Step 4. Print both boarding passes - the one which lists your real name, and the one with the name that the ticket was actually purchased under.
Step 5. Go to the airport the next day with both boarding passes.
Step 6. Present your real drivers license and modified boarding pass to the TSA checkpoint officers. Note that as they do not have access to a computer, they cannot check you against the no fly list, nor can they even verify that the name on the piece of paper matches the booking in the airline's reservation system.
Step 7. Clear security (after being frisked 5 times for looking middle eastern)
Step 8. Wait patiently at the checkin-counter, and when the gate agent announces that is time to board:
Step 9. Hand her the original boarding pass (with the fake name), which should scan perfectly, and should she even look at the computer, she'll see that the name on her screen matches the name on the boarding pass. She won't ask you for ID (as TSA already performed that task), and thus will let you on the plane.
Step 10. Board the plane, and do whatever nasty stuff you intend to do.
This is insanely easy, and unfortunately, will work.
The reasons for this massive security hole:
1. TSA agents cannot verify the authenticity of boarding passes.
2. TSA agents cannot access the airline's reservation systems, nor do a on-the-spot lookup of the ID presented to them against the no-fly-list.
3. Boarding passes are not tamper evident. One can easily edit them at home.
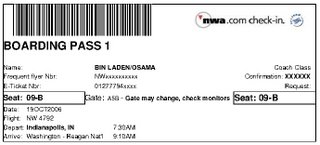
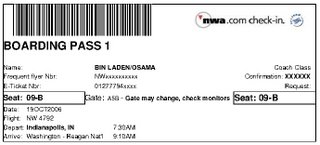
And just for fun, I thought I'd show off the modified boarding pass for my flight tomorrow. Of course, I won't be using this, as it'd guarantee me a one-way ticket straight to Gitmo. (Habeas Corpus not included):
The only way for these kind of problems to get fixed, are through through public full disclosure. TSA/DHS cannot be expected to fix anything unless they are publicly shamed into doing so.]
Shortly after 9/11, the airlines introduced a very reasonable security check (amongst a bunch of other stupid ones): They started checking ID at the gate.
It's really important to note why this is good. You see, when they scan your boarding pass, the screen will either beep yes, to tell them it's valid, or beep no, and tell them that it's a bogus pass. They'll be able to look on their terminal, see the name attached to the booking reference, and check it against the ID in front of them (ok, they rarely did this, and instead checked the name on the boarding pass - but at least they had the potential to do it correctly).
However, checking the ID of 300 passengers when you're trying to fill up and airplane can lead to considerable delays, and thus, once the hysteria of a few terrorists armed with exacto blades had calmed down, the airlines did away with this requirement, and instead offloaded it to TSA.
Herein lies the problem: TSA doesn't have access to the Airline's computer systems. Thus, they have no real way of knowing if a boarding pass is real or not. All they can do is verify that the name on the piece of paper (which may or may not be a boarding pass) matches the ID they have been given.
This situtation is made even worse when you consider the fact that you can print your own boarding pass online at home. This is often a bunch of text/html, with one or two images (a barcode, and perhaps an airline logo). It is trivially easy - as in, 20 seconds with a text-editor, and not even requiring you to open photoshop - to open it up, and change the name.
And thus, I introduce a perfectly valid method for a terrorist - known to the government, and already on the domestic no fly list, to board a US commercial flight.
Step 1. Purchase an airplane ticket in the name of "George P. Watkins"
Step 2. Check-in online the night before, and print out your boarding pass online.
Step 3. Save as HTML, edit the boarding pass code, and change it to your real name "Ali Terrorist"
Step 4. Print both boarding passes - the one which lists your real name, and the one with the name that the ticket was actually purchased under.
Step 5. Go to the airport the next day with both boarding passes.
Step 6. Present your real drivers license and modified boarding pass to the TSA checkpoint officers. Note that as they do not have access to a computer, they cannot check you against the no fly list, nor can they even verify that the name on the piece of paper matches the booking in the airline's reservation system.
Step 7. Clear security (after being frisked 5 times for looking middle eastern)
Step 8. Wait patiently at the checkin-counter, and when the gate agent announces that is time to board:
Step 9. Hand her the original boarding pass (with the fake name), which should scan perfectly, and should she even look at the computer, she'll see that the name on her screen matches the name on the boarding pass. She won't ask you for ID (as TSA already performed that task), and thus will let you on the plane.
Step 10. Board the plane, and do whatever nasty stuff you intend to do.
This is insanely easy, and unfortunately, will work.
The reasons for this massive security hole:
1. TSA agents cannot verify the authenticity of boarding passes.
2. TSA agents cannot access the airline's reservation systems, nor do a on-the-spot lookup of the ID presented to them against the no-fly-list.
3. Boarding passes are not tamper evident. One can easily edit them at home.
And just for fun, I thought I'd show off the modified boarding pass for my flight tomorrow. Of course, I won't be using this, as it'd guarantee me a one-way ticket straight to Gitmo. (Habeas Corpus not included):
Tuesday, October 17, 2006
Priceline mistake/Defcon 07
I'm a member of the flyertalk community - one of the largest online forums, and -the- place to go if you want to find out about flight/hotel deals. Due to knowledge gained there, I've flown free to Asia the last two times, to europe last summer, to Guatemala next month, and to Morocco this xmas. It's unlikely i'll be paying for international travel anytime soon.
In any case, this morning, someone posted information about a priceline mistake. Caesar's Palace in Las Vegas, for $20 per night. It seems to be a clear decimal point error (the weekend night price should be $200 per night).
With only a $25 cancellation fee, it seemed like a no brainer to go ahead, and book a 3 night stay in August 07 for Defcon.
Caesar's Palace, here I come!
(more info on the price mistake available here: http://www.flyertalk.com/forum/showthread.php?t=613722
In any case, this morning, someone posted information about a priceline mistake. Caesar's Palace in Las Vegas, for $20 per night. It seems to be a clear decimal point error (the weekend night price should be $200 per night).
With only a $25 cancellation fee, it seemed like a no brainer to go ahead, and book a 3 night stay in August 07 for Defcon.
Caesar's Palace, here I come!
(more info on the price mistake available here: http://www.flyertalk.com/forum/showthread.php?t=613722
Wednesday, October 11, 2006
Boycott the Mozilla Corp.
[Editor's note - This post was written by Chris Soghoian, the PhD student, and in no way reflects the opinions, thoughts, or policy of any of my sponsors/employers]
Firefox is now distributed by the Mozilla Corp - a for profit corporation, who, while supporting the open source development of the browser, has recently been flexing a bit of muscle.
In particular, their lawyers want linux distributions to start submitting patches to them for approval before they can be rolled out to their customer base. For critical things like security updates, this is just not possible. Distros want to roll out patches as soon as possible, and waiting for the Firefox team to OK something is just not possible.
Note, that no other open source project has tried to implement such a requirement. The Mozilla/Firefox guys are unique in this.
And essentially, what they've done is told the Debian team to fall in line (as Redhat and Novell have done), or to stop using the Firefox name and logos.
More info on this is available here http://lwn.net/Articles/200857/
Now, one interesting thing is that the Mozilla Corp makes millions of dollars per year through the google search bar in the top right hand corner of the browser. In fact, so does Apple through its Safari browser.
If you go to www.google.com, and then enter in the search, Mozilla earns nothing at all. If you use their search bar, they make a couple cents (I have no direct knowledge of the actual numbers, but they get something - and it adds up to millions of dollars when spread across all those users). This fact is public knowledge, and has been mentioned in many places: http://news.zdnet.com/2100-9588_22-6048377.html
http://www.calacanis.com/2006/03/06/firefox-mozilla-corporation-mozilla-foundation-made-72m-last/
http://www.scroogle.org/mozilla.html
http://www.techweb.com/wire/software/181501750
Now, I'm far too lazy to start going to google's homepage when I search.
So, instead, I whipped up a custom search engine for Firefox.
Simply go to this webpage http://www.dubfire.net/ffirefox, and you'll be prompted to install a new search engine for your search bar. The only difference between this custom one and the one that ships with Firefox, is that it won't identify itself to Google as coming from the Firefox toolbar. It'll look like any other search going to Google. And thus the Mozilla corp will be denied my one or two cents per search.
Sure, I like firefox. It's a great product, and far better than IE. However, it's an open sourced product, and I don't approve of them taking advantage of free community resources, debugging and code-contributions only to point their evil lawyers at Debian.
So, suck it Mozilla Corp.
Firefox is now distributed by the Mozilla Corp - a for profit corporation, who, while supporting the open source development of the browser, has recently been flexing a bit of muscle.
In particular, their lawyers want linux distributions to start submitting patches to them for approval before they can be rolled out to their customer base. For critical things like security updates, this is just not possible. Distros want to roll out patches as soon as possible, and waiting for the Firefox team to OK something is just not possible.
Note, that no other open source project has tried to implement such a requirement. The Mozilla/Firefox guys are unique in this.
And essentially, what they've done is told the Debian team to fall in line (as Redhat and Novell have done), or to stop using the Firefox name and logos.
More info on this is available here http://lwn.net/Articles/200857/
Now, one interesting thing is that the Mozilla Corp makes millions of dollars per year through the google search bar in the top right hand corner of the browser. In fact, so does Apple through its Safari browser.
If you go to www.google.com, and then enter in the search, Mozilla earns nothing at all. If you use their search bar, they make a couple cents (I have no direct knowledge of the actual numbers, but they get something - and it adds up to millions of dollars when spread across all those users). This fact is public knowledge, and has been mentioned in many places: http://news.zdnet.com/2100-9588_22-6048377.html
http://www.calacanis.com/2006/03/06/firefox-mozilla-corporation-mozilla-foundation-made-72m-last/
http://www.scroogle.org/mozilla.html
http://www.techweb.com/wire/software/181501750
Now, I'm far too lazy to start going to google's homepage when I search.
So, instead, I whipped up a custom search engine for Firefox.
Simply go to this webpage http://www.dubfire.net/ffirefox, and you'll be prompted to install a new search engine for your search bar. The only difference between this custom one and the one that ships with Firefox, is that it won't identify itself to Google as coming from the Firefox toolbar. It'll look like any other search going to Google. And thus the Mozilla corp will be denied my one or two cents per search.
Sure, I like firefox. It's a great product, and far better than IE. However, it's an open sourced product, and I don't approve of them taking advantage of free community resources, debugging and code-contributions only to point their evil lawyers at Debian.
So, suck it Mozilla Corp.
Sunday, October 08, 2006
Knives on a ********** plane
Last year, while travelling on Air Deccan, a low-cost airline in India, I carried a pocket knife onboard the airplane.... The story is far more interesting than that summary alone, and I highly recommend you read the full writeup here:
http://slightparanoia.blogspot.com/2006/02/chennaiport-blair.html
The photographic evidence of the event is here:
A knife on the plane:
http://www.flickr.com/photos/csoghoian/120651089/
Sealing the locks to prove that they haven't been tampered with:
http://www.flickr.com/photos/csoghoian/120650920/
However, that was India - and this is America... land of the free, home of the brave - and more importantly, home of TSA - who is supposed to be protecting you from big bad terrorists.
It's common knowledge that a tiny fraction of the checked luggage (which is just a few feet below the passengers in the airplane's hold) is actually x-rayed.
On top of that, it's also common knowledge that the airlines only perform passenger matching on bags for one airplane trips: i.e. if you don't get on the airplane on a trip from Indy->DC, then they pull your bag off at the last minute. However, if you get on the airplane from Indy->DC, and then leave the airport instead of getting on your connecting flight from DC->San Francisco, they let the bag go on the next flight. A terrorist would simply put a timed bomb in their bag, and have it explode during the second flight.
However, lets ignore those facts for now.. and focus on what TSA is supposed to be good at... keeping liquids, nail clippers, and weapons out of the airplane cabin.
My girlfriend visited me this weekend, and accidentally left a sharp paring knife in her carry-on bag.. both ways (i.e. DC->Indy, and Indy->DC). It was only once she got back to DC this evening that she realized what happened.
And guess what... TSA didn't notice at all.
For the record, as much of a troublemaker as I am, my girlfriend wasn't trying to test TSA. She is a law-abiding citizen, and simply overlooked the knife in the rush to pack her (messy) bag for her flight....
The evidence is here:
http://www.flickr.com/photos/katmandoo/264556078/
http://slightparanoia.blogspot.com/2006/02/chennaiport-blair.html
The photographic evidence of the event is here:
A knife on the plane:
http://www.flickr.com/photos/csoghoian/120651089/
Sealing the locks to prove that they haven't been tampered with:
http://www.flickr.com/photos/csoghoian/120650920/
However, that was India - and this is America... land of the free, home of the brave - and more importantly, home of TSA - who is supposed to be protecting you from big bad terrorists.
It's common knowledge that a tiny fraction of the checked luggage (which is just a few feet below the passengers in the airplane's hold) is actually x-rayed.
On top of that, it's also common knowledge that the airlines only perform passenger matching on bags for one airplane trips: i.e. if you don't get on the airplane on a trip from Indy->DC, then they pull your bag off at the last minute. However, if you get on the airplane from Indy->DC, and then leave the airport instead of getting on your connecting flight from DC->San Francisco, they let the bag go on the next flight. A terrorist would simply put a timed bomb in their bag, and have it explode during the second flight.
However, lets ignore those facts for now.. and focus on what TSA is supposed to be good at... keeping liquids, nail clippers, and weapons out of the airplane cabin.
My girlfriend visited me this weekend, and accidentally left a sharp paring knife in her carry-on bag.. both ways (i.e. DC->Indy, and Indy->DC). It was only once she got back to DC this evening that she realized what happened.
And guess what... TSA didn't notice at all.
For the record, as much of a troublemaker as I am, my girlfriend wasn't trying to test TSA. She is a law-abiding citizen, and simply overlooked the knife in the rush to pack her (messy) bag for her flight....
The evidence is here:
http://www.flickr.com/photos/katmandoo/264556078/
Friday, October 06, 2006
TSA followup
Mr Harris, the TSA person whose business card I had been given never got back to me. Thus, after waiting 2 weeks, I decided to go ahead and contact his boss. This afternoon, I had a telephone conversation with Rich Adams, the Assistant Federal Security Director for Law Enforcement at TSA's Indianapolis Airport office.
The main points of the conversation were as follows:
TSA has many different configurations of checkpoints. At the gate/terminal that I went through, they have designed a special streamlined channel for SSSS (secondary screening passengers) to go through. They do not have enough physical space to allow for these SSSS people to opt for a manual pat down.
Other airports/terminals, where the SSSS people go through the same lines as everyone else may have more space, and thus, may allow people to opt out of being puffed by the creepy Smiths/GE entryscan machines.
The highlight of the conversation, for me, was after this;
Him: (the above bit of text, telling me why I could not decline to get puffered at this checkpoint if i was designated SSSS).
Me: Could you please send me that in writing, and include a copy of the specific regulation or law which documents and backs up that policy.
Him: No. It's classified as SSI (Sensitive Security Information).
Me: What? That doesn't seem fair. You're forcing me to follow a rule or law yet are not permitting me to see the text of the law. How can I know if your employees are following it properly?
Him: For security reasons, we do not allow this information to be made public.
Me: Have you heard of the book Catch 22 by Joseph Heller?
Him: Yes
Me: Does this not seem a bit similar, or perhaps, alternatively, to something by Kafka?
Him: *losing patience - he then reminds me of the TSA mission of keeping us safe, and that his employees are not out to hinder our "god given" rights*
I also complained about having to go up to 2 levels of supervisor to be able to take sex lube on the plane- even though this was listed as an acceptable item on their website.
He didn't seem to have any problems with this, and essentially said that they were always doing their best to educate their staffmembers, and that me pulling 2 supervisors over was a normal part of the security screening process.
Quite a fun conversation, i'd say.
Remember Kids: You're either with us, or are helping the terrorists.
The main points of the conversation were as follows:
TSA has many different configurations of checkpoints. At the gate/terminal that I went through, they have designed a special streamlined channel for SSSS (secondary screening passengers) to go through. They do not have enough physical space to allow for these SSSS people to opt for a manual pat down.
Other airports/terminals, where the SSSS people go through the same lines as everyone else may have more space, and thus, may allow people to opt out of being puffed by the creepy Smiths/GE entryscan machines.
The highlight of the conversation, for me, was after this;
Him: (the above bit of text, telling me why I could not decline to get puffered at this checkpoint if i was designated SSSS).
Me: Could you please send me that in writing, and include a copy of the specific regulation or law which documents and backs up that policy.
Him: No. It's classified as SSI (Sensitive Security Information).
Me: What? That doesn't seem fair. You're forcing me to follow a rule or law yet are not permitting me to see the text of the law. How can I know if your employees are following it properly?
Him: For security reasons, we do not allow this information to be made public.
Me: Have you heard of the book Catch 22 by Joseph Heller?
Him: Yes
Me: Does this not seem a bit similar, or perhaps, alternatively, to something by Kafka?
Him: *losing patience - he then reminds me of the TSA mission of keeping us safe, and that his employees are not out to hinder our "god given" rights*
I also complained about having to go up to 2 levels of supervisor to be able to take sex lube on the plane- even though this was listed as an acceptable item on their website.
He didn't seem to have any problems with this, and essentially said that they were always doing their best to educate their staffmembers, and that me pulling 2 supervisors over was a normal part of the security screening process.
Quite a fun conversation, i'd say.
Remember Kids: You're either with us, or are helping the terrorists.
Tuesday, October 03, 2006
A dystopian view of personal Tivos
At some point not to long into the future, we'll have personal recorders for our lives. The first versions will record all the audio we hear, and later, as storage/cpu becomes cheap, they'll start to record video too.
The killer technology that'll enable this will be speech recognition tech that actually works.
You'll carry this device on your person, it'll record all of the conversations that you participate in, will convert those to text which you'll then be able to easily search later.
This will solve that ever annoying problem of not being able to quite remember what so-and-so told you the other day. You'll just need to remember a couple of the words from the conversation and will be easily be able to go back and locate the conversation...
The other obvious benefit to this will be that you'll be able to easily figure out which song you heard on the radio, coming out of someone's car, or that you danced to in the Club. Song recognition technology is already out there, and so it's quite easy to imagine that this'd be rolled into such a device.
Due to the need to turn this info into searchable text, you're going to need to upload it somewhere for processing. It'll either be uploaded in real time over wireless/cellular networks, or maybe you'll dock the device at the end of your day for processing. Either way, it doesn't really matter for the purposes of this blog post.
Now, consider the fact that pretty much everyone has a cellphone on them. Cellphones all include GPS chips now - for E911 reasons (although, it's interesting to note that the ever-present greed of the cellphone companies is the main barrier to us having access to this GPS data right now. They want to make a buck each time you use this data to interact with a merchant).
And herein lies the problem. Consider the following scenario:
A crime occurs. The police contact the phone companies and get a list of everyone who was nearby to the crime when it happened (which they're able to get via the GPS/cell tower log data). Now, the feds demand that each person hand over the audio/video data from their personal Tivos so that they can piece together information on the crime.
This seems like a great idea. Right? Except when you consider the fact that large portions of society do not like the Police (this is due to many reasons - racial profiling, past abuses by the police, drug war overzealousness, etc).
If you witness a crime right now, it is quite easy for you to tell the police that you don't remember seeing anything. The real memories are your own, and so you have solid control over who you share these with.
Fast forward to the digital age of the personal Tivo - and suddenly, you do not have the right to keep this information from the police anymore.
Remember that you can only plead the 5th if you risk incriminating yourself. If you are incriminating someone else, you have no right to stay silent, nor keep your data to yourself.
Encryption - the magic pixie dust that has solved so many of the Security World's problems thus far, fails us... because the police can compel you to disclose your keys.
There are systems in place (StegFS, The Rubberhose filesystem) which aim to protect you against Rubber Hose Attacks (i.e. you being beaten by a CIA interrogator until you disclose your personal data). They work by essentially allowing you to say "I don't have any data on the disk"... Or by allowing you to have multiple encrypted files, one encrypted with your "real" key, and the other with a key which you give to the police when asked..
However, in the case of the personal tivo - through the GPS records that the Feds will gain from the phone companies, the police will know exactly where you are and when. Thus, if you give them bogus data, and they know you were walking past the Clocktower at noon - and your Tivo data does not have a clock chiming noon, they'll know you've given them false data.
Thus, we have an even more extreme form of the rubberhose attack. How do you protect your data from the police when they can 1. compel you to give it to them, and 2. They have a fair idea of at least some portion of the data on your disk? They can use what they know to verify if the data you later give them is in fact real.
It's a puzzling problem - and it's going to become real.... It's just a matter of time.
How do we solve this problem? I have no idea.
The killer technology that'll enable this will be speech recognition tech that actually works.
You'll carry this device on your person, it'll record all of the conversations that you participate in, will convert those to text which you'll then be able to easily search later.
This will solve that ever annoying problem of not being able to quite remember what so-and-so told you the other day. You'll just need to remember a couple of the words from the conversation and will be easily be able to go back and locate the conversation...
The other obvious benefit to this will be that you'll be able to easily figure out which song you heard on the radio, coming out of someone's car, or that you danced to in the Club. Song recognition technology is already out there, and so it's quite easy to imagine that this'd be rolled into such a device.
Due to the need to turn this info into searchable text, you're going to need to upload it somewhere for processing. It'll either be uploaded in real time over wireless/cellular networks, or maybe you'll dock the device at the end of your day for processing. Either way, it doesn't really matter for the purposes of this blog post.
Now, consider the fact that pretty much everyone has a cellphone on them. Cellphones all include GPS chips now - for E911 reasons (although, it's interesting to note that the ever-present greed of the cellphone companies is the main barrier to us having access to this GPS data right now. They want to make a buck each time you use this data to interact with a merchant).
And herein lies the problem. Consider the following scenario:
A crime occurs. The police contact the phone companies and get a list of everyone who was nearby to the crime when it happened (which they're able to get via the GPS/cell tower log data). Now, the feds demand that each person hand over the audio/video data from their personal Tivos so that they can piece together information on the crime.
This seems like a great idea. Right? Except when you consider the fact that large portions of society do not like the Police (this is due to many reasons - racial profiling, past abuses by the police, drug war overzealousness, etc).
If you witness a crime right now, it is quite easy for you to tell the police that you don't remember seeing anything. The real memories are your own, and so you have solid control over who you share these with.
Fast forward to the digital age of the personal Tivo - and suddenly, you do not have the right to keep this information from the police anymore.
Remember that you can only plead the 5th if you risk incriminating yourself. If you are incriminating someone else, you have no right to stay silent, nor keep your data to yourself.
Encryption - the magic pixie dust that has solved so many of the Security World's problems thus far, fails us... because the police can compel you to disclose your keys.
There are systems in place (StegFS, The Rubberhose filesystem) which aim to protect you against Rubber Hose Attacks (i.e. you being beaten by a CIA interrogator until you disclose your personal data). They work by essentially allowing you to say "I don't have any data on the disk"... Or by allowing you to have multiple encrypted files, one encrypted with your "real" key, and the other with a key which you give to the police when asked..
However, in the case of the personal tivo - through the GPS records that the Feds will gain from the phone companies, the police will know exactly where you are and when. Thus, if you give them bogus data, and they know you were walking past the Clocktower at noon - and your Tivo data does not have a clock chiming noon, they'll know you've given them false data.
Thus, we have an even more extreme form of the rubberhose attack. How do you protect your data from the police when they can 1. compel you to give it to them, and 2. They have a fair idea of at least some portion of the data on your disk? They can use what they know to verify if the data you later give them is in fact real.
It's a puzzling problem - and it's going to become real.... It's just a matter of time.
How do we solve this problem? I have no idea.
Subscribe to:
Posts (Atom)